I am often asked by clients how they can provide additional levels of controls to their Security and Compliance privileged roles to mitigate the risks of excessive, unnecessary, or misused access permissions to important resources.
Microsoft recommends the following best practice for managing privileged accounts:
- Use least privileged access
- Turn on multi-factor authentication for all your administrator accounts
- Use Privileged Identity Management to grant just-in-time access with optional approvals
- Configure recurring access reviews to revoke unneeded permissions over time
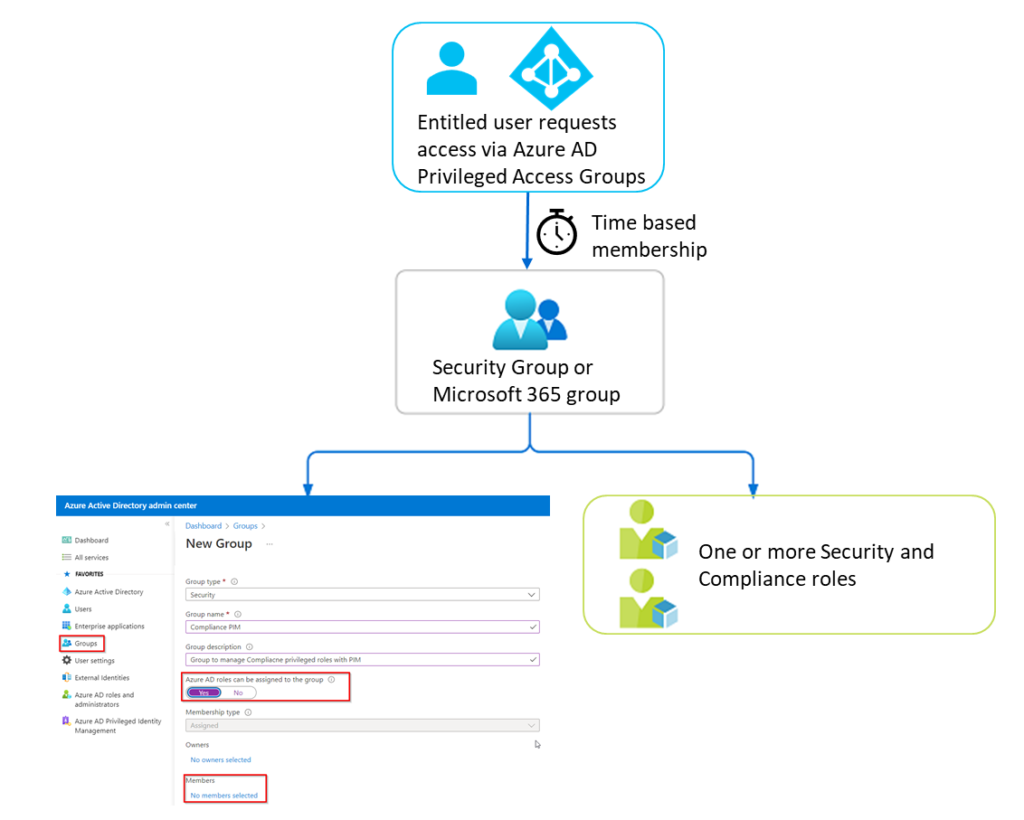
If you have Azure AD Premium 2 licensing you can use Azure AD Privilege Identity Management (PIM) to provide just-in-time access to privileged admin accounts. PIM only provides just-in-time access to Azure AD and Azure privileged roles. The issue with Security and Compliance roles is that they are managed in Security and Compliance admin Centers and not in Azure AD.
So how can we protect Security and Compliance roles with just-in-time access to mitigate the risks of excessive, unnecessary, or misused access permissions to important resources?
Read on to discover how to use Privileged Access Groups in PIM to indirectly provide just-in-time access to your Security & Compliance roles. In addition, this process will work with other non-Azure AD roles such as roles from Exchange or SharePoint.
…
Read More